Use Cases for the Teams Doing the Real Work of Security
We’re proud to call the San Francisco Bay Area home (yes, we love Karl the Fog). But our team comes from across the globe, united by one shared mission: to rethink cybersecurity from the ground up.
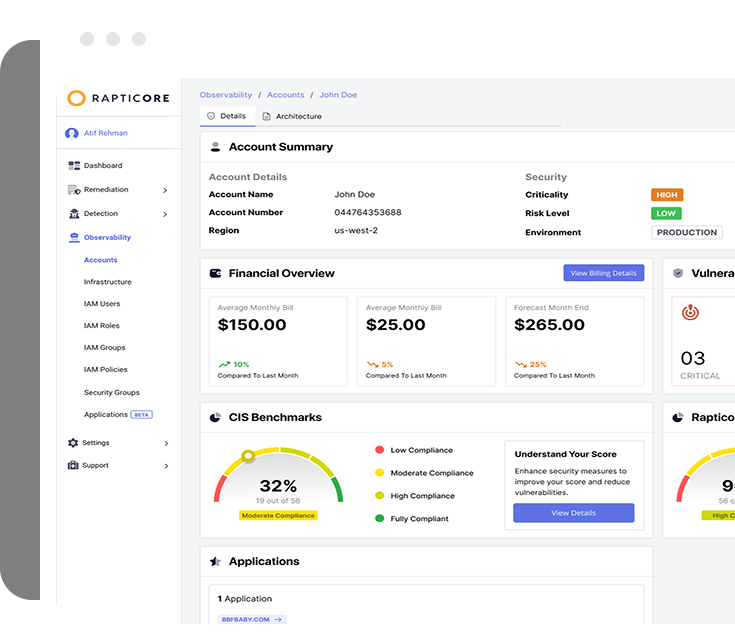
Cloud Risk Visibility for Confident Leadership
Rapticore delivers real-time metrics, KPIs, and KRIs that help CISOs and security leaders answer the cloud risk question with clarity. Our layered dashboards cut through complexity, offering end-to-end visibility and measurable insights into program performance.

Actionable Dashboards
One command center for risk, posture, and trends
Layered Disclosure
Simplified views of complex environments
KPI & KRI Tracking
Quantify security performance over time
Click-to-Context Navigation
Instantly access what’s highly relevant
Move from Detection to Action—Fast!
Speed is everything in the early stages of incident response. Rapticore’s contextual asset inventory and config search help teams move faster, understand scope, and reduce dwell time—enabling quicker response, smarter containment, and effective eviction planning.
Relationship Mapping
See how assets and users connect
State-Aware Search
Query the environment by config and condition
Lateral Movement View
Visualize potential attacker paths
Rapid Eviction Planning
Contain threats with greater confidence
More Coverage, Less Overwhelm
AppSec teams are stretched thin. Rapticore inventories cloud apps, code, and CI/CD pipelines, automatically models threat surfaces, and consolidates risk—all in one place. That means stronger security with fewer manual hours.
Automated Threat Modeling
STRIDE-based design risk assessment
Code & Cloud Inventory
Full visibility across the SDLC
CI/CD-Aware Insights
Security that understands how you deploy
IAM Right-Sizing
Detect and reduce over-permissioned access
Prioritize What Matters. Ignore the Noise
Vulnerability management never ends—but it can get smarter. Rapticore blends CVSS, threat intel, and asset context to prioritize risks with precision. Teams focus only on what’s exploitable, impactful, and worth fixing now.
Contextual Scoring
More than CVSS—real-world relevance
SSVC-Based Triage
Prioritization by stakeholder impact
Live Asset Awareness
Know the state of what you’re securing
Threat Intel Fusion
CVEs enriched with real-time attacker data
Rapticore does more than alert you. It fixes, guides, and adapts.
All-in-one security that thinks for itself—so you don’t have to babysit it.